View of Ubiquitous tools, connected things and intelligent agents: Disentangling the terminology and revealing underlying theoretical dimensions | First Monday

THE FINTECH DISRUPTION OF THE BANKING SYSTEM: THE «OMNI DIGITAL BANK CUSTOMER» | FERNANDO JIMENEZ MOTTE

Ubiquitous computing. Types of Computing 1. Mainframe era (many people, one computer) 2. PC era (one person, one computer) transition phase ( the internet, - ppt download

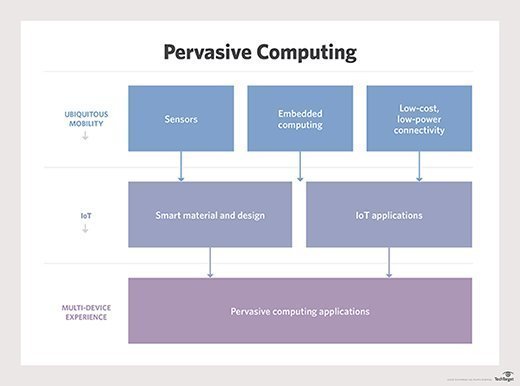
The example of Pervasive Computing Applications with Fusion Techniques | Download Scientific Diagram
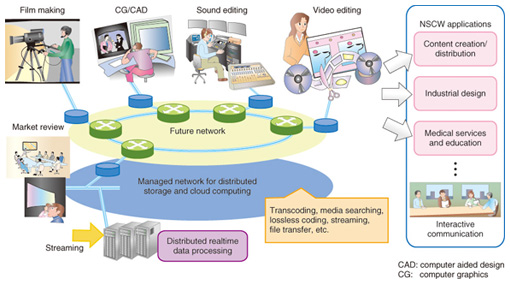
Secure Method of Managing Digital Content in Ubiquitous Computing Environment | NTT Technical Review












.jpg)



![PDF] A Ubiquitous Computing environment for aircraft maintenance | Semantic Scholar PDF] A Ubiquitous Computing environment for aircraft maintenance | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/32847a8f9a1065b2829fa9fa33f94f6720f05698/3-Figure2-1.png)