Why is the SHA-256 hash function impossible to reverse? I saw the mathematics of 'how to manually convert a text to SHA-256' here: https://qvault.io/cryptography/how-sha-2-works-step-by-step-sha-256/ Can't we just go backwards? - Quora
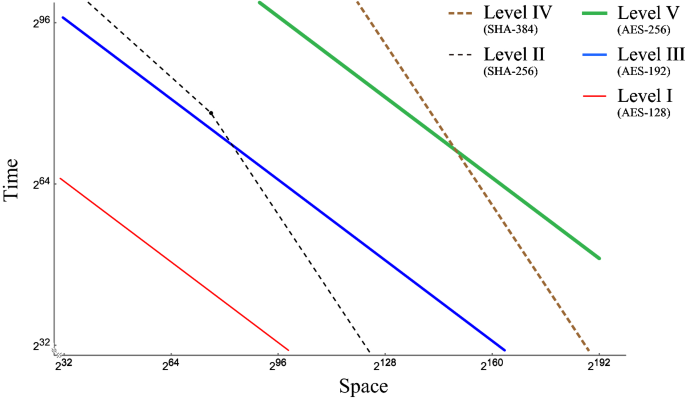
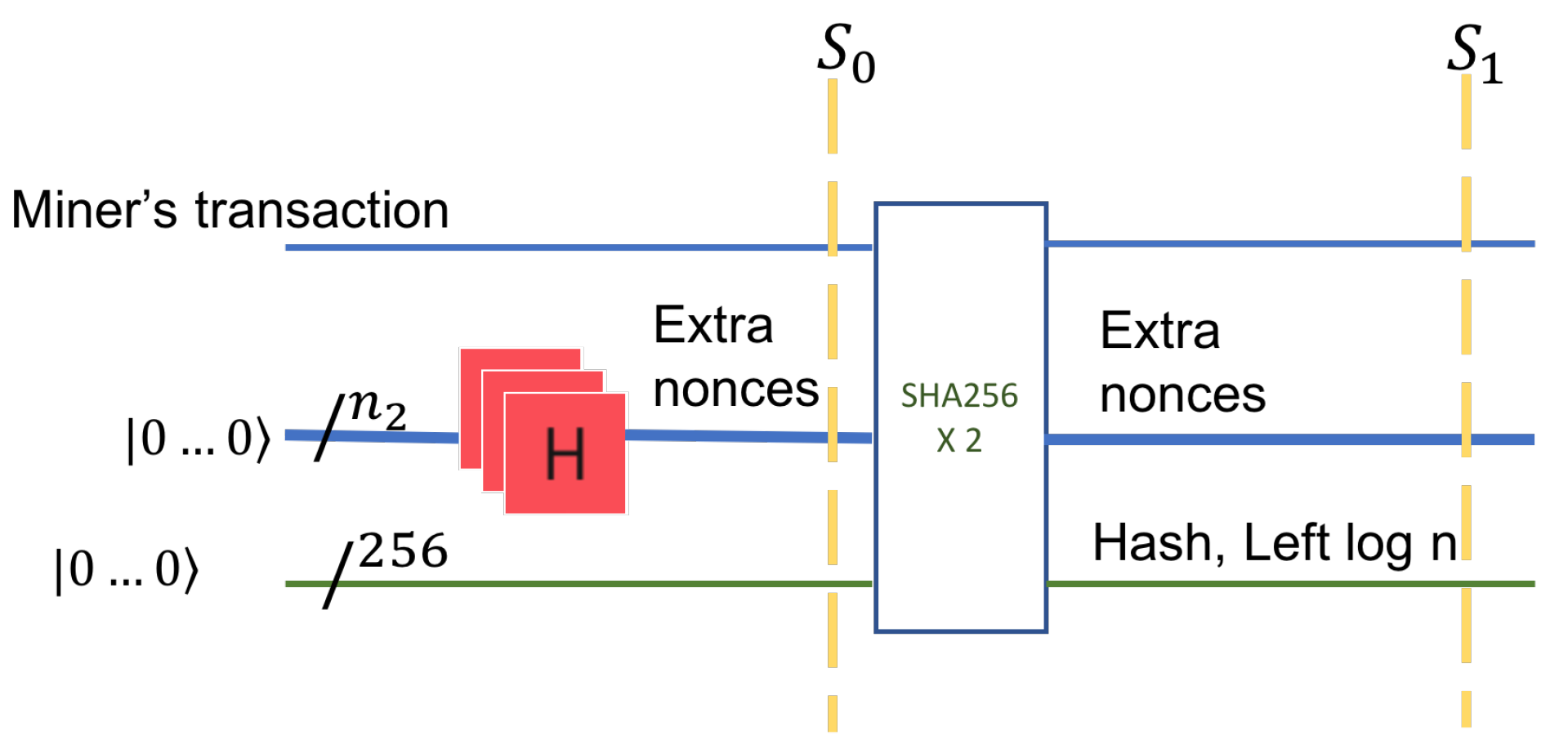
Time–space complexity of quantum search algorithms in symmetric cryptanalysis: applying to AES and SHA-2 | SpringerLink

Lukasz Olejnik (@LukaszOlejnik@Mastodon.Social) on Twitter: "Hypothetical quantum computers could break current encryption, RSA-1024 in a day, AES (128) in 600 years. SHA256 is safe. Solution: more funding to post-quantum cryptography, and quantum

Researchers have created a new and potentially dangerous encryption-breaking quantum algorithm | TechSpot

Scientists estimate that quantum computers may become powerful enough to crack the Bitcoin encryption in a decade - NotebookCheck.net News
4 Quantum Computing's Implications for Cryptography | Quantum Computing: Progress and Prospects |The National Academies Press

a Round operations and b message schedule of SHA-256 algorithm. Each... | Download Scientific Diagram