YAVIS Codeschloss Türöffner Zutrittskontrollsystem Sicherheit Tor Eintrag + 10 Schlüsselanhänger RFID Nähe Türeinstieg Standalone Access Control System für 1000 Benutzer : Amazon.de: Baumarkt
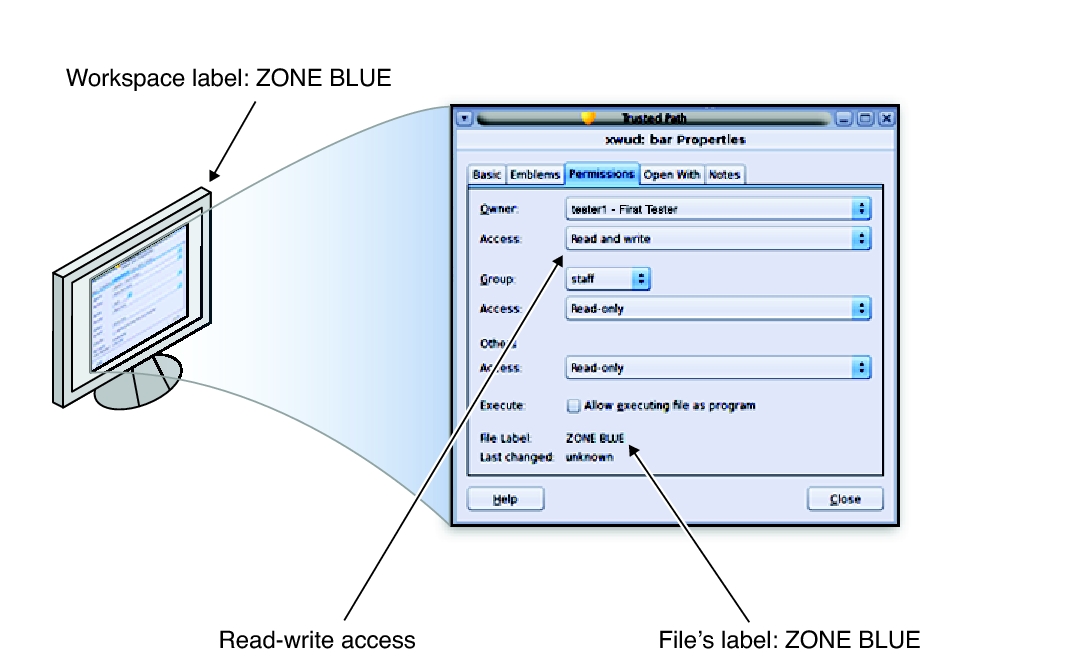
How to programmatically control access to files in C# using FileSecurity objects - technical-recipes.com

Lunaz finalizes UEV testing program at Millbrook Proving Ground | Automotive Testing Technology International
ISO 27001 Annex : A.9.4.4 Use of Privileged Utility Programs & A.9.4.5 Access Control to Program Source Code | Infosavvy Security and IT Management Training