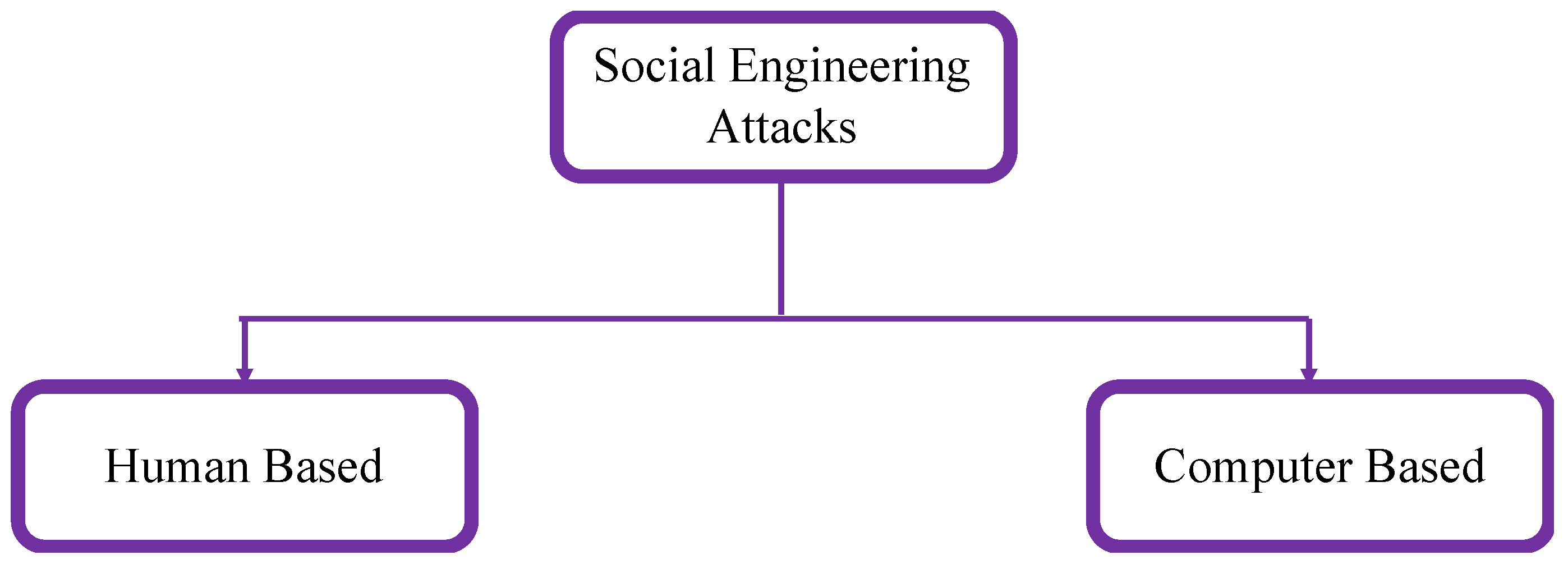
BAI514 – Security I. Social Engineering Social engineering involves obtaining protected information from individuals by establishing relationships with. - ppt download

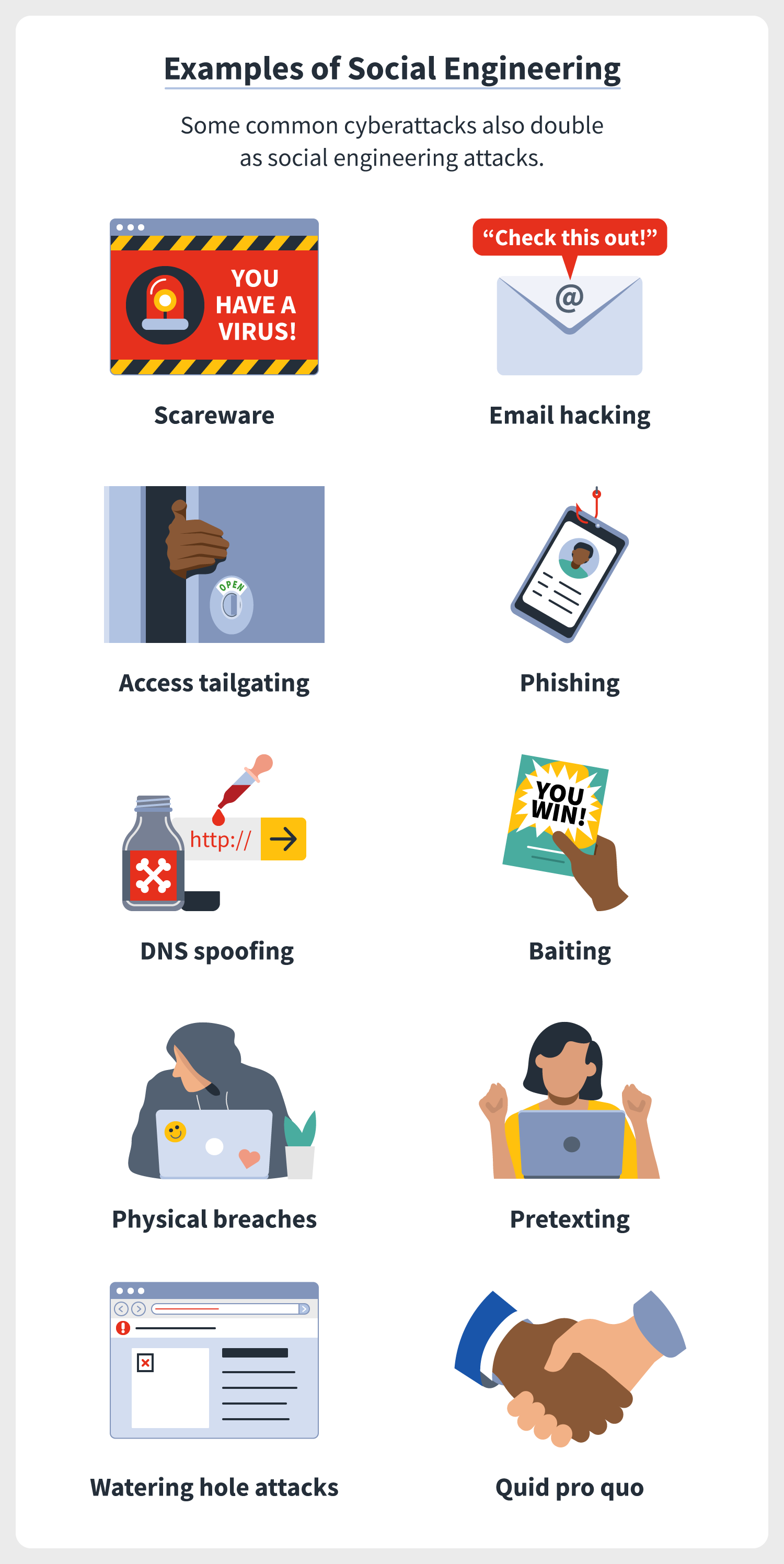
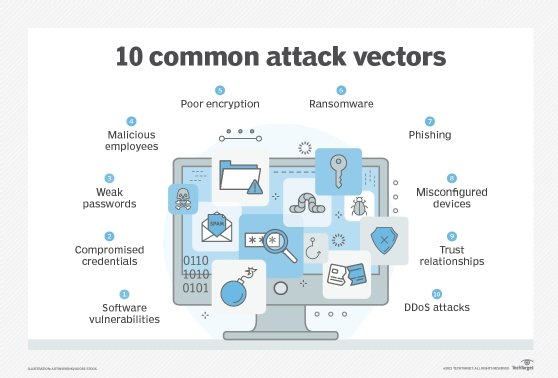
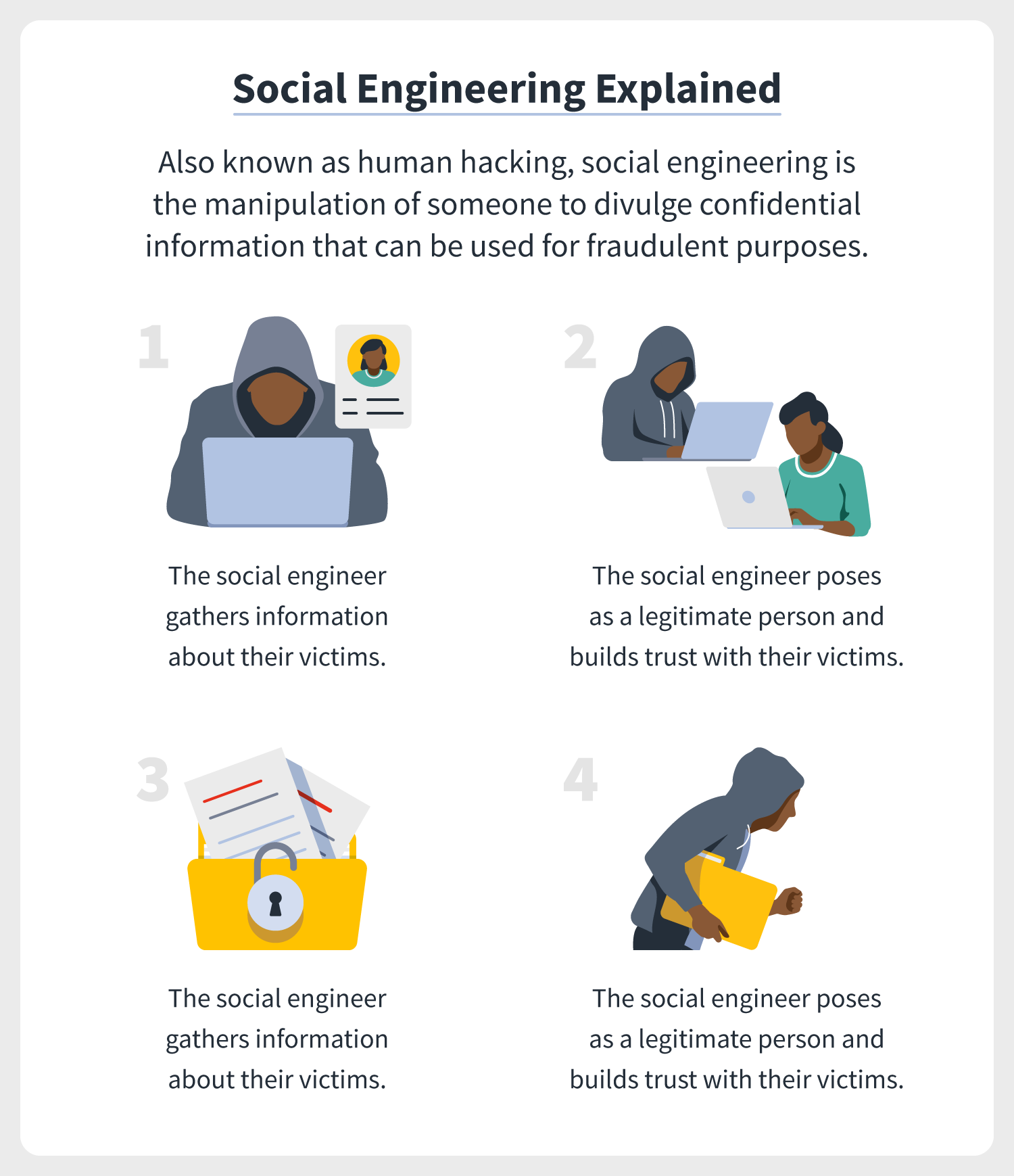
What Is Social Engineering? Definition, Types, Techniques of Attacks, Impact, and Trends - Spiceworks
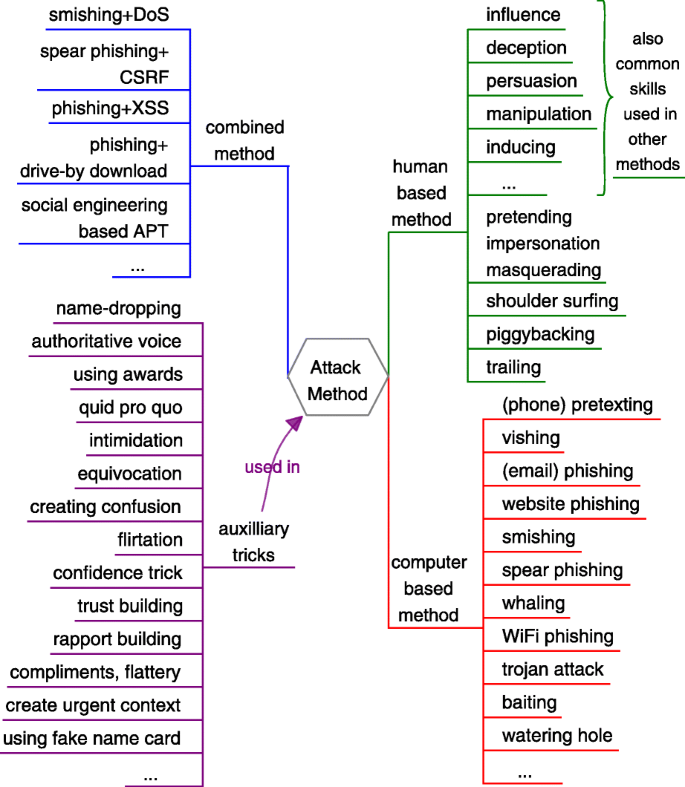
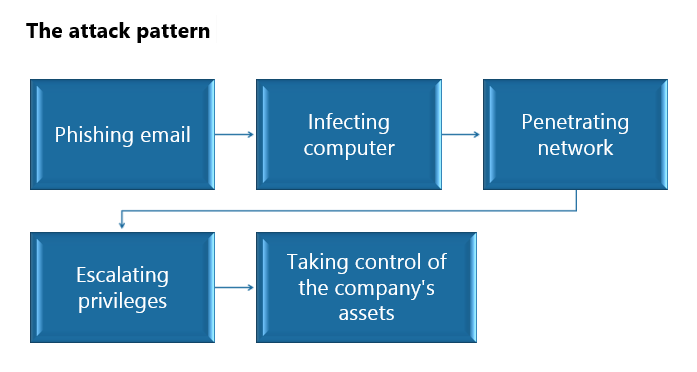
Social engineering in cybersecurity: a domain ontology and knowledge graph application examples | Cybersecurity | Full Text


![PDF] Social engineering in social networking sites: Affect-based model | Semantic Scholar PDF] Social engineering in social networking sites: Affect-based model | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/8563d22f4cd2625bd9ca751136a520f3e0517de5/6-Table1-1.png)