How to Catch Broken Access Control Security Vulnerabilities in Code Review Part 2 | PullRequest Blog

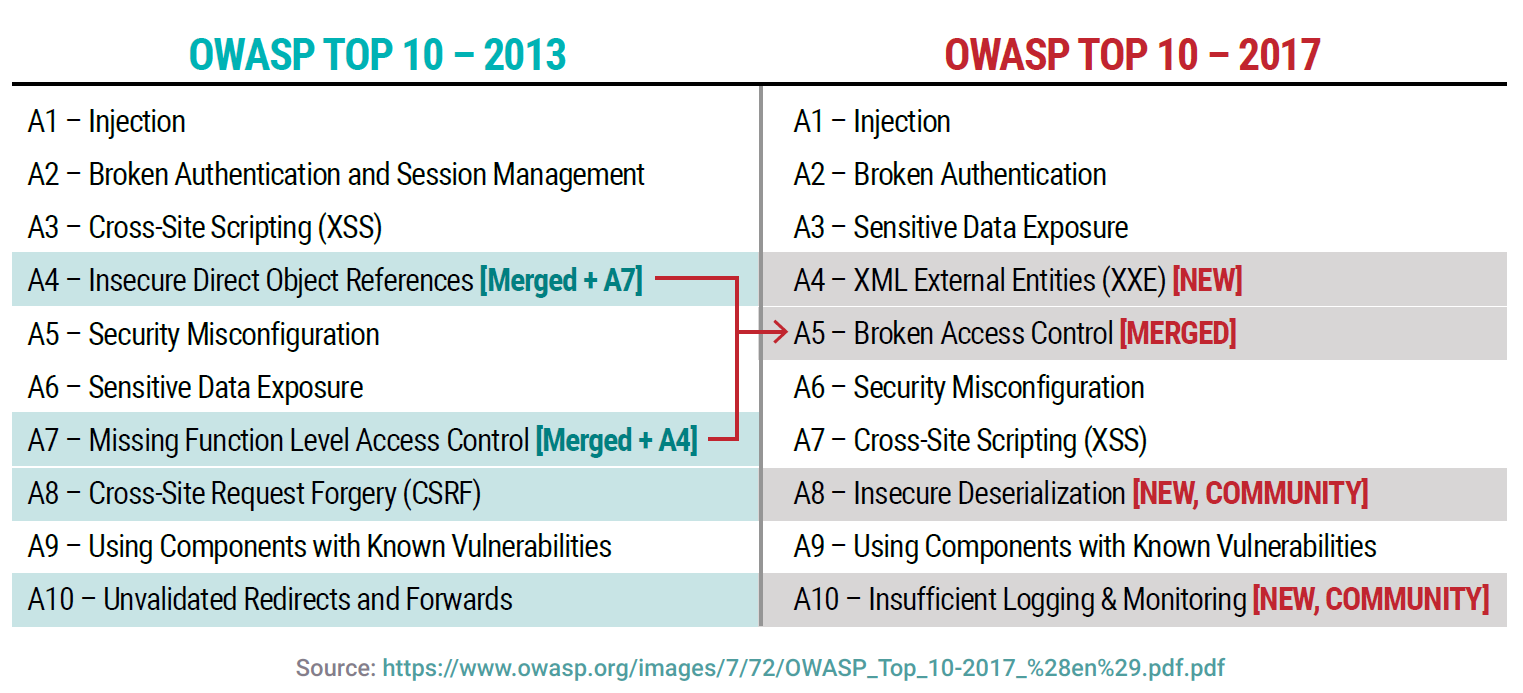
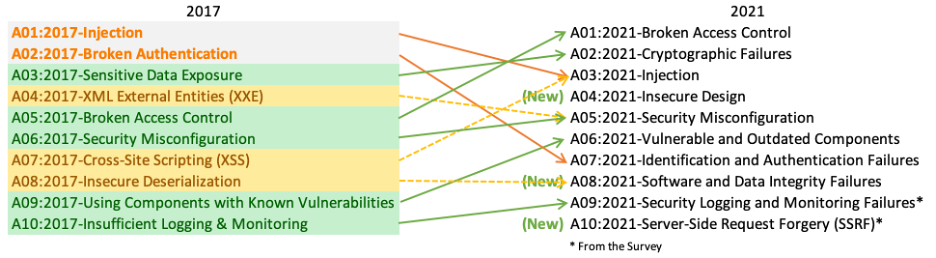
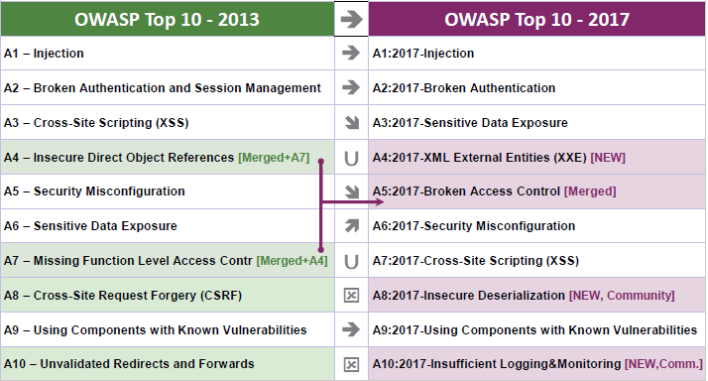
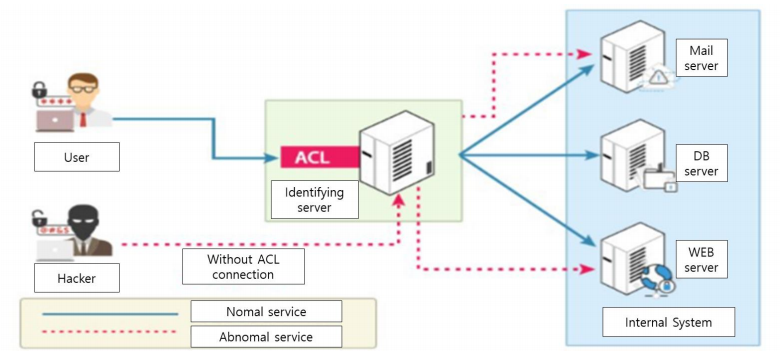
Malaysia IT Professional Network - Broken Access Control is listed under OWASP Top 10, thus the need for web security is real. To gain more on the best practices to combat incoming

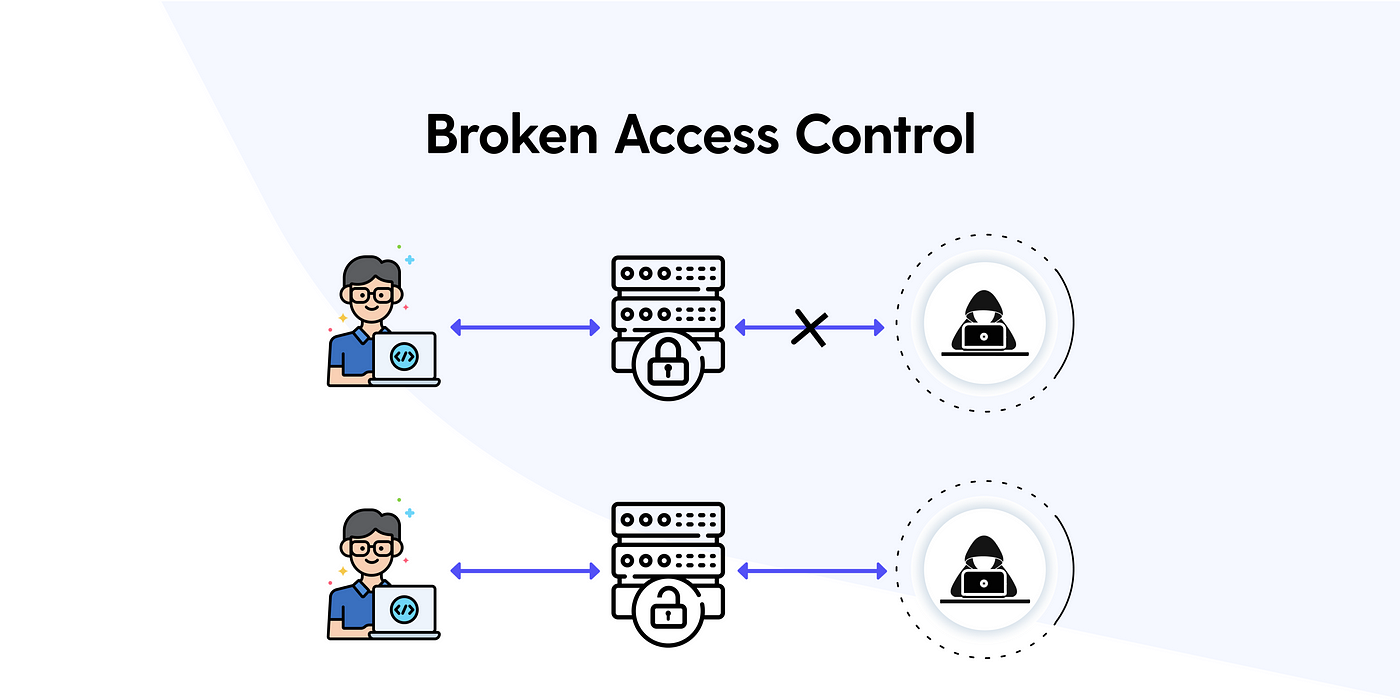
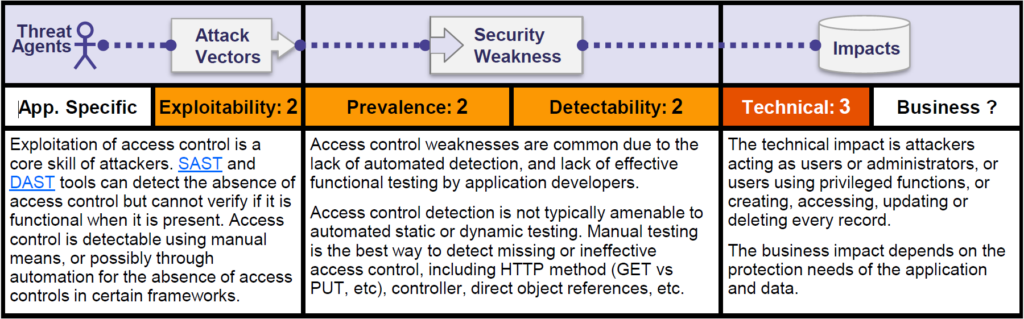
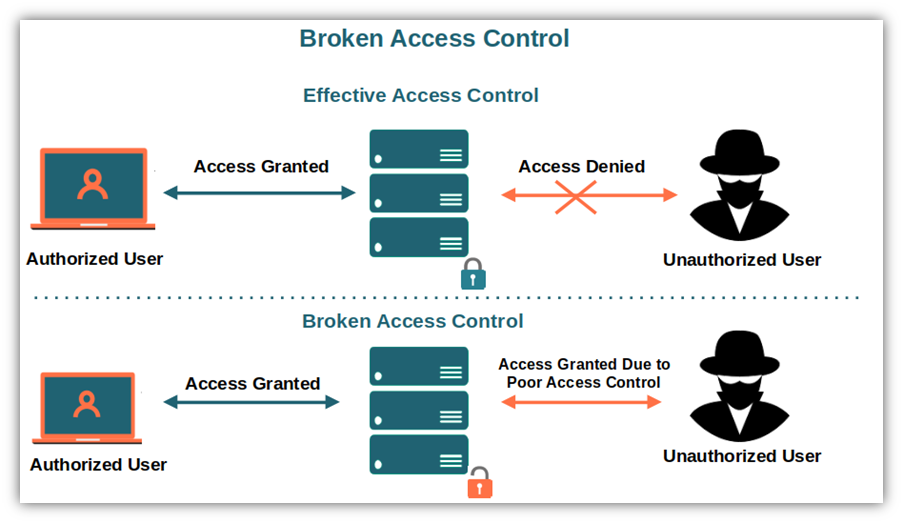
OWASP Top 10: #5 Broken Access Control and #6 Security Misconfiguration (2019) Online Class | LinkedIn Learning, formerly Lynda.com